ICSForge has been released under the GPLv3 license — an open-source tool for validating the coverage of cybersecurity tools in industrial control systems (ICS). The platform generates realistic industrial traffic and PCAP files, and maps each scenario to the MITRE ATT&CK for ICS v18 matrix. The declared coverage is 68 techniques out of 83, or 82 %.
Version 0.62 supports ten industrial protocols: Modbus/TCP, DNP3, IEC-104 (IEC 60870-5-104), S7comm, OPC UA, EtherNet/IP, BACnet/IP, MQTT, IEC 61850 GOOSE, and PROFINET DCP. Each protocol comes with 5 to 36 traffic variants, for a total of 536 single-step scenarios and 11 ready-made multi-step attack chains.
How it works
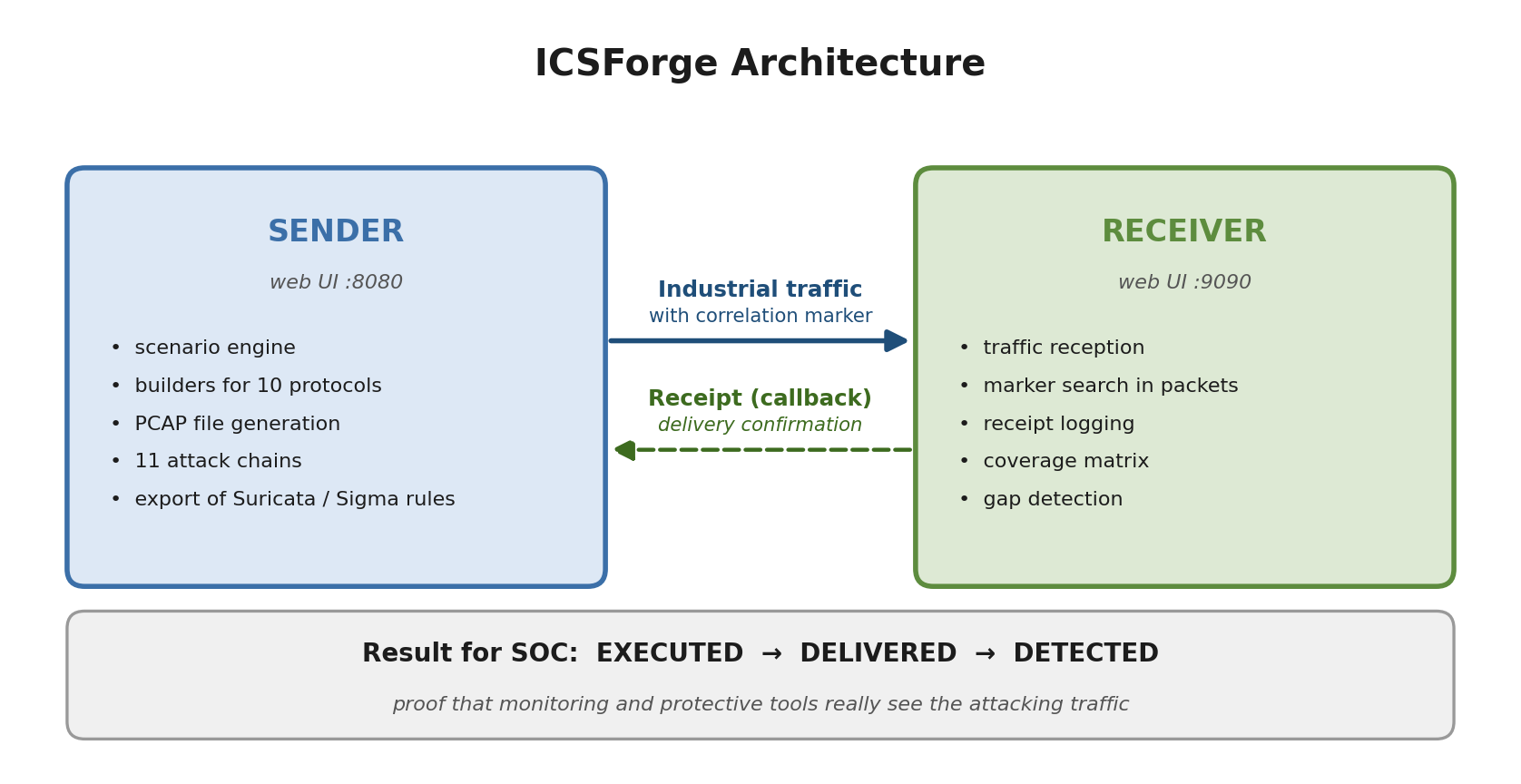
The platform is built around two interacting components — a sender and a receiver. The sender generates traffic and embeds a correlation marker into every packet. The receiver, deployed in the segment under test, looks for this marker and sends a receipt back. If the receipt arrives, the packet reached its destination over the wire. If a monitoring system deployed in the same segment reacted to the traffic, detection works. This produces an unambiguous chain: executed → delivered → detected. For cases where the very presence of the marker would taint the experiment, a stealth mode is provided — the wire carries byte-realistic frames with no traces of ICSForge.
What MITRE ATT&CK for ICS is
MITRE ATT&CK for ICS is an open knowledge base maintained since 2020 by MITRE, an American non-profit corporation. It is a structured catalogue of techniques an adversary uses when attacking industrial control systems, built on the analysis of real incidents in power, oil & gas, water utilities and manufacturing. MITRE ATT&CK for ICS is an open knowledge base maintained since 2020 by MITRE, an American non-profit corporation. It is a structured catalogue of techniques an adversary uses when attacking industrial control systems, built on the analysis of real incidents in power, oil & gas, water utilities and manufacturing.
The base is split into 12 tactics — categories of an attacker's goals: gain Initial Access, achieve Persistence, evade detection (Evasion), inhibit protective functions (Inhibit Response Function), influence the process (Impair Process Control), and so on. Each tactic contains specific techniques describing how it can be achieved: for example, T0855 "Unauthorized Command Message" — an unauthorized setpoint or control command, T0832 "Manipulation of View" — falsifying data shown to the operator. As of today, the matrix lists 83 unique techniques.
For the industry, the matrix has become a standard language for describing threats and assessing security posture. Modern passive network monitors (NSM), ICS firewalls, and SIEM systems tag their detection rules with ATT&CK technique IDs — this lets vendors be compared and a security programme to be laid out on a clear coordinate grid. ICSForge uses the same grid from the other side: for every technique that can be reproduced at the network level, the platform provides one or several ready-made scenarios.
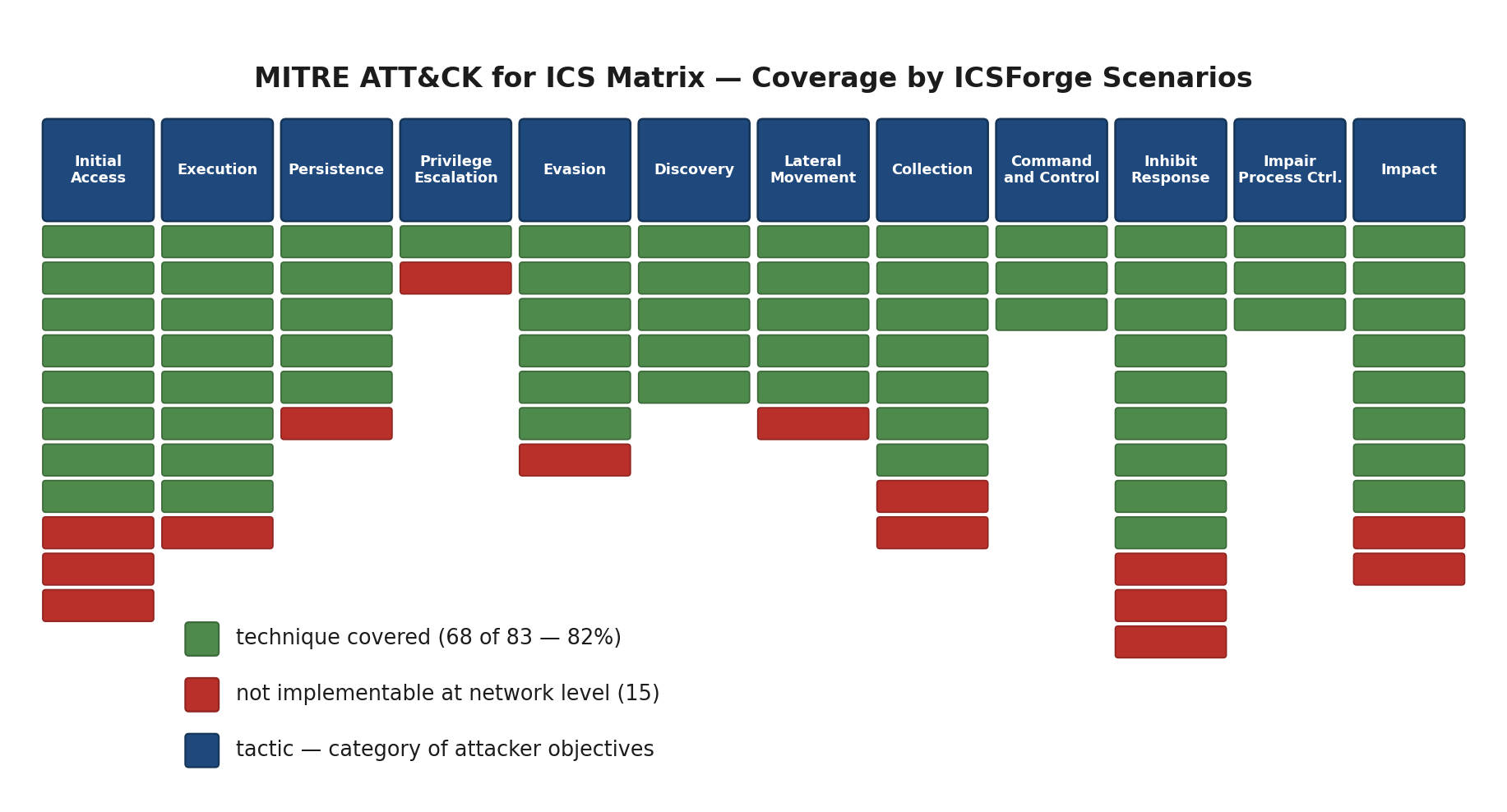
Out of 83 techniques, the platform implements 68. The remaining 15 are techniques requiring physical access or leaving no observable network footprint: the authors honestly classify these as "not implementable at the network level" and provide a justification for each in an open configuration file. Such transparency is uncommon among tools of this class.
Ready-made attack chains
In addition to single techniques, ICSForge contains 11 multi-step scenarios modelling known public attacks. Among them — Industroyer2 (a combination of IEC-104 and S7comm), TRITON-style chains (targeting safety instrumented systems), Stuxnet (manipulation of a Siemens PLC programme), a scenario based on the Oldsmar incident (alteration of water-treatment setpoints), as well as a "full ICS Kill Chain" — from reconnaissance to impact.
What Industroyer is
Industroyer (also known as CrashOverride) is the first publicly known piece of malware originally developed specifically to attack electric power facilities. It was used in December 2016 in the partial blackout of northern Kyiv and supported the protocols IEC 60870-5-101, IEC 60870-5-104, IEC 61850, and OPC DA — i.e. the same set normally used in substation automation. Industroyer2 is a variant discovered in April 2022 during an attempted attack on the Ukrainian power grid: it contained hard-coded configurations for a specific facility and operated exclusively over IEC-104. Reproducing the network traffic characteristic of these attacks in a controlled environment is a standard task in SOC readiness assessment, and ICSForge provides a tool for it that requires neither real malware samples nor access to them.
Additional capabilities and safety
In addition to traffic generation, ICSForge automatically generates detection rules for Suricata and Sigma in three tiers — from laboratory rules that catch the platform's own marker, to semantic rules intended for production use that trigger on specific application-layer function codes and services.
To prevent accidental launch in a production network, by default outbound traffic is allowed only to RFC 1918, loopback and TEST-NET addresses; access to public addresses is blocked. Authentication in the web interface is mandatory, passwords are stored using scrypt, and receipt delivery is protected by a dedicated token. The authors explicitly emphasise: ICSForge does not exploit vulnerabilities, does not modify the state of real devices and does not model any physical impact on the process — it is a tool for assessing the quality of detection, not for attacking.
The platform is written in Python 3.10+, supports deployment from source and via Docker Compose; the command-line interface has full parity with the web UI.
The project repository is available here.